General Discussion
Related: Editorials & Other Articles, Issue Forums, Alliance Forums, Region ForumsResearch at Stanford University..metadata does betray sensitive details
Warnings that phone call “metadata” can betray detailed information about your life has been confirmed by research at Stanford University. Researchers there successfully identified a cannabis cultivator, multiple sclerosis sufferer and a visitor to an abortion clinic using nothing more than the timing and destination of their phone calls.
Jonathan Mayer and Patrick Mutchler, the researchers behind the finding, used data gleaned from 546 volunteers to assess the extent to which information about who they had called and when revealed personally sensitive information.
The research aimed to answer questions raised by the NSA wiretapping revelations, where it was revealed that the US intelligence agency collects metadata - but not content - of millions of phone calls on mobile networks.
No harm?
The researchers cite statements like that of President Obama, that the NSA was “not looking at content,” and ask whether the legal distinction between metadata and content is matched by harm reduction in the real world.
“Is it easy to draw sensitive inferences from phone metadata,” they ask. “How often do people conduct sensitive matters by phone, in a manner reflected by metadata?”
http://www.theguardian.com/technology/2014/mar/13/phone-call-metadata-does-betray-sensitive-details-about-your-life-study
The Stasi and Metadata
The East German secret police, known as the Stasi, were an infamously intrusive secret police force. They amassed dossiers on about one quarter of the population of the country during the Communist regime.
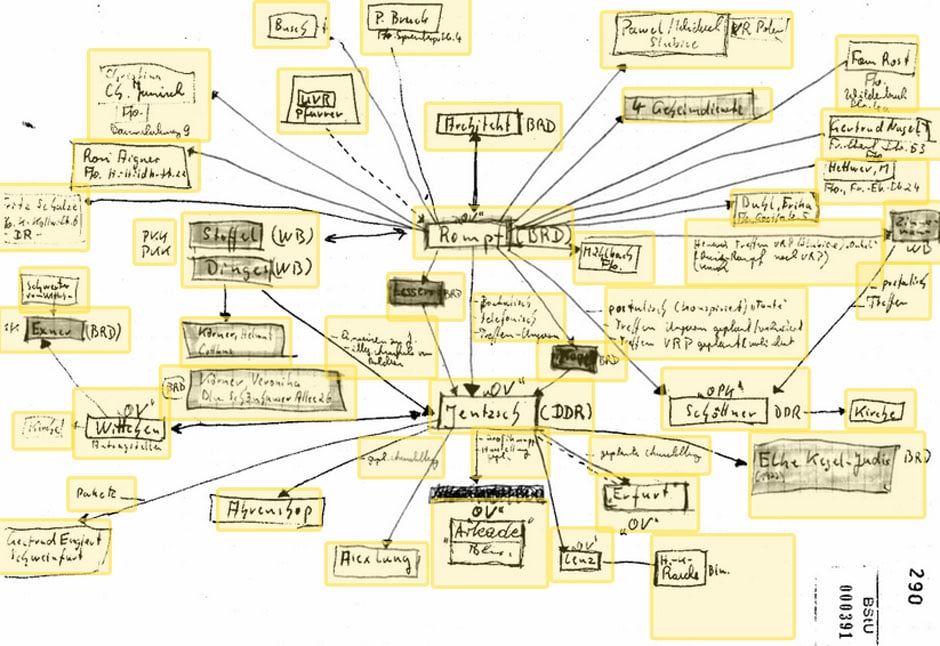
But their spycraft — while incredibly invasive — was also technologically primitive by today’s standards. While researching my book Dragnet Nation, I obtained the above hand drawn social network graph and other files from the Stasi Archive in Berlin, where German citizens can see files kept about them and media can access some files, with the names of the people who were monitored removed.
The graphic shows forty-six connections, linking a target to various people (an “aunt,” “Operational Case Jentzsch,” presumably Bernd Jentzsch, an East German poet who defected to the West in 1976), places (“church”), and meetings (“by post, by phone, meeting in Hungary”).
Gary Bruce, an associate professor of history at the University of Waterloo and the author of “The Firm: The Inside Story of the Stasi,” helped me decode the graphic and other files. I was surprised at how crude the surveillance was. “Their main surveillance technology was mail, telephone, and informants,” Bruce said.
Another file revealed a low-level surveillance operation called an IM-vorgang aimed at recruiting an unnamed target to become an informant. (The names of the targets were redacted; the names of the Stasi agents and informants were not.) In this case, the Stasi watched a rather boring high school student who lived with his mother and sister in a run-of-the-mill apartment. The Stasi obtained a report on him from the principal of his school and from a club where he was a member. But they didn’t have much on him — I’ve seen Facebook profiles with far more information.
http://www.propublica.org/article/how-the-stasi-spied-on-social-networks
marions ghost
(19,841 posts)The Dragnet Nation book is very good.
reddread
(6,896 posts)KoKo
(84,711 posts)Ichingcarpenter
(36,988 posts)showing the metadata they complied on a 'person of interest'