Here's some very old news; quite boring isn't it?In the FBI We Trust?
The FBI is one of several federal agencies participating in the "War of Ideas" in an ongoing battle against terrorism, which is a vague legal term, as put forth in The U.S.A. Patriot Act II. One of the earliest devices the FBI began using is a software tool that existed well before Sept. 11, 2001, called CARNIVORE. Briefly, Carnivore is a program that monitors Web sites, networks and email for a broad range of content.
Carnivore software copies, sends and then reconstructs data that passes through a network, including Web postings, Web pages, email messages, and file downloads. For example, the FBI might use Carnivore to capture an email message traveling from a computer through an ISP network. If Carnivore works properly, neither sender nor recipient know that detection software is copying an email message. FBI officials describe Carnivore as a software tool that hunts down and chews up data. In an attempt to decrease public apprehension over Carnivore, especially images the system name calls up, the FBI officially renamed the system DSC1000. Even so, "Carnivore" is still how the media and public refer to the system. Here's the next generation but still quite dated, don't you agree?Echelon & The NSA
Certain Web sites claim, Carnivore is only a tip of the iceberg when it comes to Internet surveillance. The secretive NSA (National Security Administration) operates a monitoring system called Echelon that can globally search every email message and piece of Internet data for keywords, such as "bomb." Echelon is reportedly a joint surveillance network operated by the United States, Great Britain, Canada, Australia, and New Zealand to name a few.
U.S. governmental agencies refused comment on whether Echelon exists. In 2000, the NSA blocked a congressional inquiry seeking details about Echelon.
Evidence also points to existence of another NSA surveillance project, reportedly code-named Tempest, that captures computer keystrokes and monitor images, even if the capturing computer is in another location and not connected in any way to the targeted computer.Who knows what software is in use these days? I mean, let's get real. Who even cares?
We burried countless fine Americans for this next silly piece of crap but again, who cares? War is a tough game, right moms and dads? When do you think they'll start the draft again?Amendment IV (the Fourth Amendment) of the United States Constitution is an integral part of the Bill of Rights that guards against unreasonable search and seizure. As mid-wife to liberty, it arose in response to controversial Writs of Assistance, widely abused by agents of King George. This broadly applied general search warrant became a significant trigger of the American Revolution.
The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated, and no Warrants shall issue, but upon probable cause, supported by oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.The Supreme Court has held the rule does not apply only in certain situations: (1) probation or parole revocation hearings; (2) tax hearings; (3) deportation hearings; (4) when government officials illegally seize evidence outside the United States; (5) when a "private actor" (not a State employee) illegally seizes evidence; or (6) when illegally seized evidence impeaches defendant testimony. Furthermore, a defendant can object to the admission of unconstitutionally seized evidence only if such seizure violates personal Fourth Amendment rights. Defendants can not assert the rights of a third party.
Closely related to the exclusionary rule is the "fruit of the poisonous tree" doctrine, which prohibits the government from introducing any evidence obtained subsequent to or resulting from illegal searches.
Here's some more old news but who has time to worry about or even read this silly little modern law?Section-by-Section Analysis of Justice Department draft "Domestic Security Enhancement Act of 2003," also known as "PATRIOT Act II" (2/14/2003)
The Department of Justice (DOJ) has been drafting comprehensive anti-terrorism legislation for the past several months. The draft legislation, dated January 9, 2003, grants sweeping powers to the government, eliminating or weakening many of the checks and balances that remained on government surveillance, wiretapping, detention and criminal prosecution even after passage of the USA PATRIOT Act, Pub. L. No. 107-56, in 2001.
Among its most severe problems, the bill
Diminishes personal privacy by removing checks on government power...
Permits the government, under certain circumstances, to bypass the Foreign Intelligence Surveillance Court altogether...
Shelters federal agents engaged in illegal surveillance without a court order from criminal prosecution if they are following orders of high Executive Branch officials...
Creates a new category of "domestic security surveillance" that permits electronic eavesdropping of entirely domestic activity under very loose standards...
Uses an overbroad definition of terrorism that covers an ever-increasing group, including people engaging in certain forms of peaceful protest...
Provides for general surveillance orders covering multiple functions of high tech devices...
Creates a new, separate crime of using encryption technology that adds five years to any sentence for crimes committed with a computer...
Expands nationwide search warrants to the extent that they no longer meet even broad definitions of terrorism in the USA PATRIOT Act...
Gives the government secret access to credit reports without consent or even judicial process...
Enhances government abilities to obtain sensitive information without any prior judicial approval...
Permits, without any connection to anti-terrorism efforts, sensitive personal information about U.S. citizens to be shared with a variety of outside organizations...
Terminates court-approved limits on police spying, initially put in place to prevent McCarthy-style law enforcement and persecution based on political or religious affiliations...
Permits searches, wiretaps and surveillance of United States citizens on behalf of foreign governments - including dictatorships and human rights abusers - in the absence of Senate-approved treaties...
http://www.aclu.org/safefree/general/17203leg20030214.html
At least I've got a new picture for you folks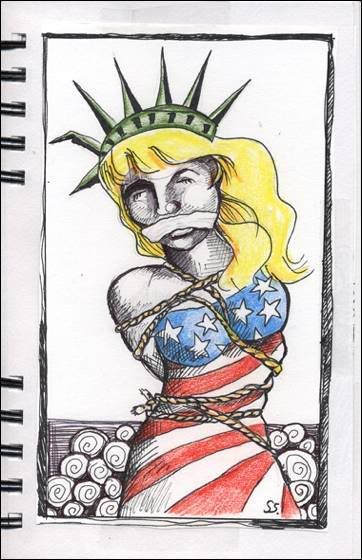 sorry to waste your time on things that matter so little in modern America. Have a nice day!
sorry to waste your time on things that matter so little in modern America. Have a nice day!